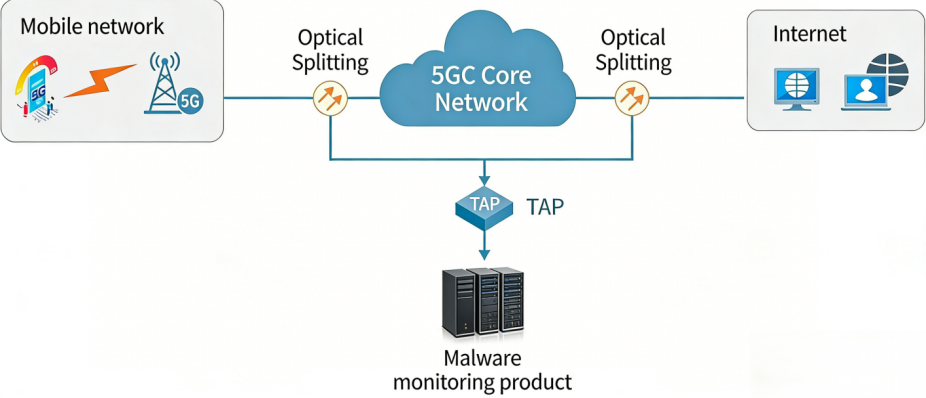
The Mobile Internet DPI (Deep Packet Inspection) and Network Visualization Analysis Platform is deployed at the core network nodes of mobile operators. It is designed for monitoring and managing network traffic in various core networks, including 4G and 5G, primarily serving telecommunications operators and relevant regulatory bodies, ensuring compliance with industry standards and performance evaluation requirements.
The Mobile Internet DPI (Deep Packet Inspection) and Network Visualization Analysis Platform is deployed at the core network nodes of mobile operators. It is designed for monitoring and managing network traffic in various core networks, including 4G and 5G, primarily serving telecommunications operators and relevant regulatory bodies, ensuring compliance with industry standards and performance evaluation requirements.
The Mobile Internet DPI and Network Visualization Analysis Platform consists of several modules, including the signaling plane analysis module, user plane analysis module, sample restoration module, sample scanning engine, traffic management engine, and analytics module. It supports the detection of anomalies such as malicious program propagation, traffic anomalies, and network behavior analysis, generating event logs based on detected incidents. It also enables the capture and restoration of samples for further analysis, facilitating the identification and management of related events.
This system is deployed at the core network nodes of operators' mobile Internet infrastructure, supporting the monitoring and management of network traffic in 4G, 5G, and other core network environments. It primarily serves telecommunications operators and regulatory bodies, ensuring compliance with international industry standards.
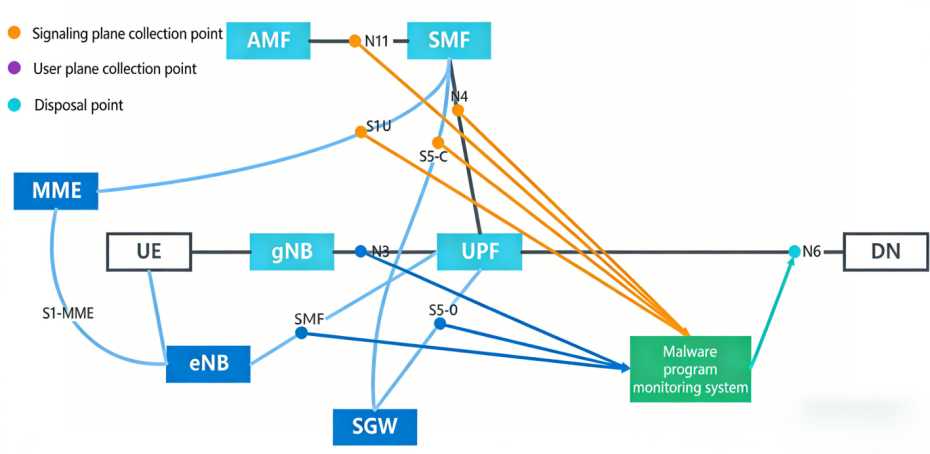
Since certain user data, such as from N3 (S1-U/) interfaces, lacks user identification or location information, the platform retrieves user data from other interfaces (e.g., N4, N11, S11, S5-C) to correlate and enrich this data.
The Mobile Internet DPI and Network Visualization Analysis Platform is compatible with both traditional x86 servers and alternative architecture servers, including Kunpeng, Feiteng, and Haiguang, offering robust cross-platform compatibility. The platform delivers leading performance and functionality and has earned high recognition within the telecommunications industry.
Protocol Recognition and Event Analysis
Traffic Management and Incident Handling
High Performance and Accurate Detection
Comprehensive Traffic and Communication Relationship Discovery
Preprocessing
Traffic Behavior Analysis
Sample Restoration
Traffic Management and Incident Handling
Feature Database Management